-
Bogon IP Address Meaning, Working, Risks and Ranges

The bogon ip address may look strange to some networks, and its usage can be very crucial in detecting suspicious traffic. It might seem to be merely another technical term at first sight, but, in fact, it can be deeply related to the process of assigning and controlling IP ranges as it is done by
-
What Is Private DNS and how does it secure your Internet
The internet seems easy to use at the tip of the iceberg, but much goes on under the carpet whenever you open a web page. Each search, every click, every page open relies on the system at interrelating names with numbers. Nevertheless, the majority of the population does not consider the way in which this
-
Ipv4 and Ipv6 diagram Explained for Network Basics
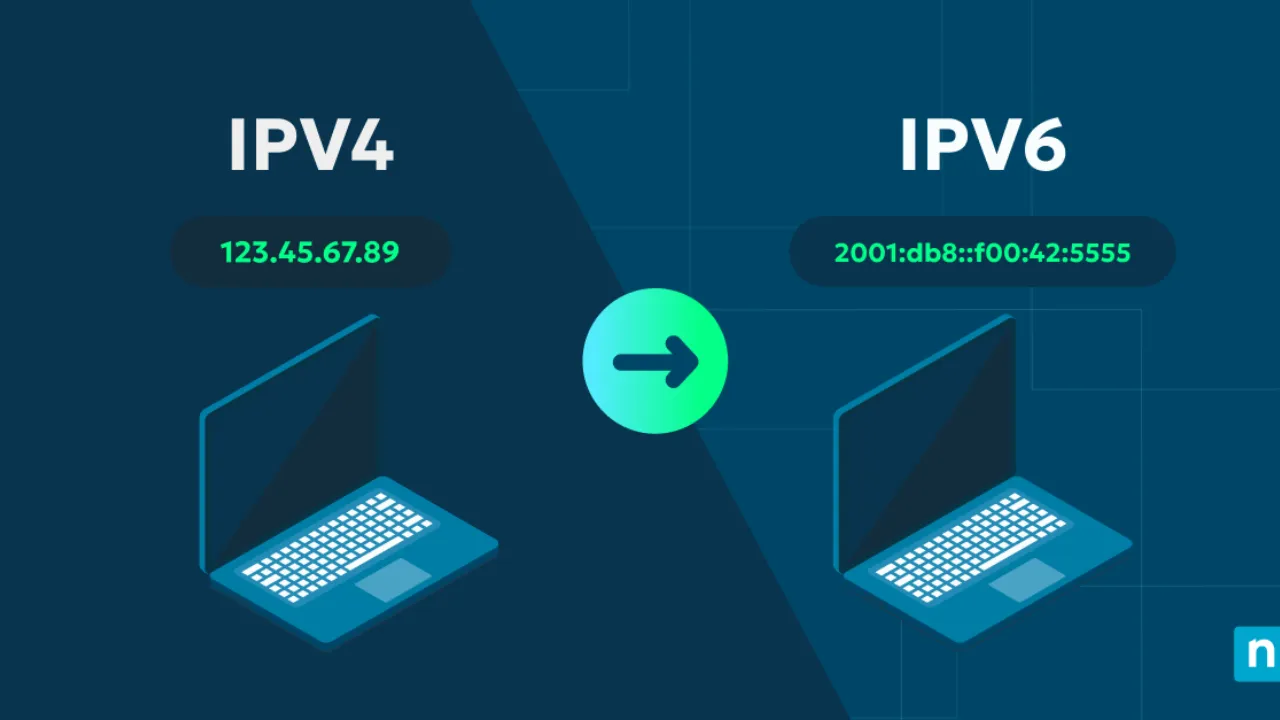
The Internet is based on structured communication, with each packet having a specific format. That format becomes easier to understand when you study an ipv4 and ipv6 diagram in a simplified way. Most learners are initially confused by the appearance of this structure, as it does not appear to be technical, but you can easily
-
How to Use Google Authenticator Transfer on New Phone

Upgrading your phone feels refreshing, yet it often brings hidden technical challenges. One of the most essential activities is the security app management. It goes unnoticed by many users until a time when they experience problems with their logins and realize just how important it is. It is precisely in that respect that how to
-
Thread in Java with Clear Lifecycle, Examples And Creation Methods

Modern software does not run one task at a time anymore. Users expect speed, smooth interaction, and real-time updates. That is why developers rely on concurrency to deliver better performance. A strong understanding of thread in java helps you design applications that feel fast and responsive even under heavy load. At first, Threading can initially
-
Types of Operating System Explained for Modern Use

Today, technology is more than ever before, and most users barely consider the question of what makes their gadgets work at the back end. Even opening an app, or even just saving a file, all of it is dependent on a system that occurs behind-the-scenes. This system is called the operating system. Understanding the types
-
ERR_SSL_PROTOCOL_ERROR Fix Steps for Secure Access
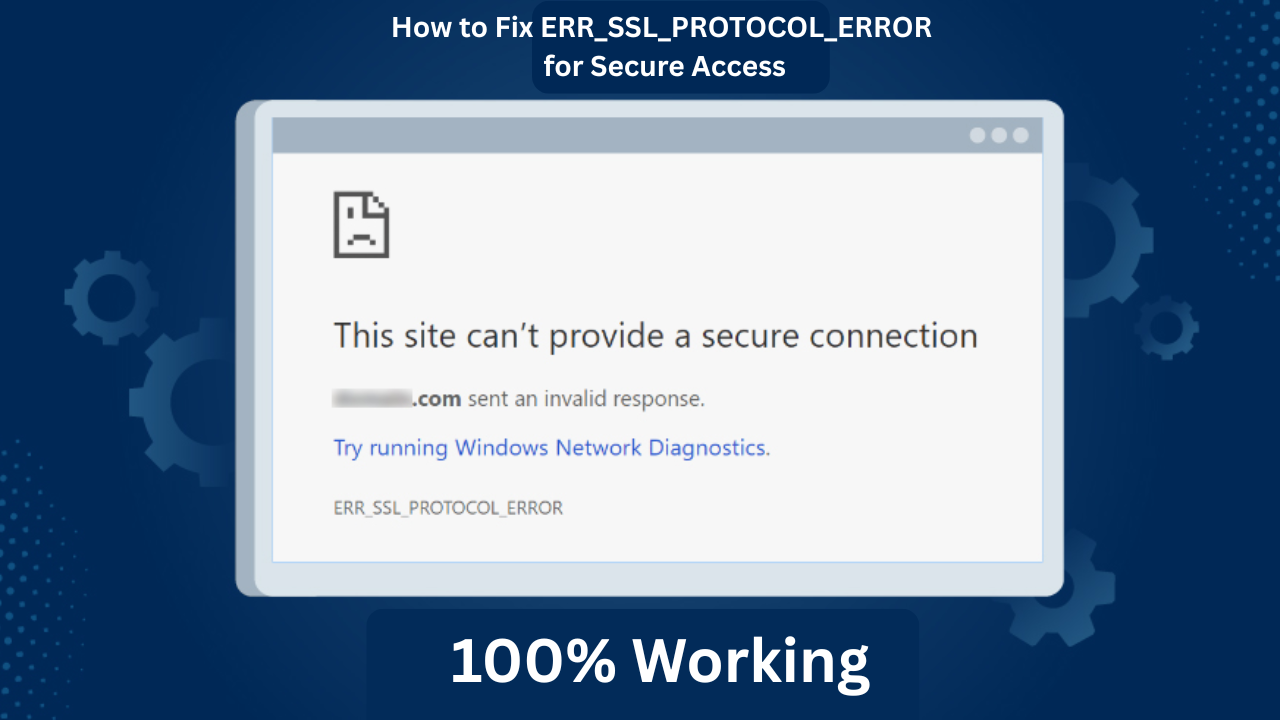
A website should open smoothly, yet sometimes it suddenly stops and shows a security warning instead. Such an experience can be confusing to users since the page appears normal, but it prevents further access with the message of err_ssl_protocol_error. This problem is observed when a browser fails to connect to a secure site; yet the
-
IPv4 vs IPv6: Complete Guide to Modern IP Networking
The internet may feel simple on the surface, yet a powerful system runs behind every click and every connection. Internet Protocol is at the heart of this system and makes sure that devices communicate with one another in an unambiguous manner. In this article, you will have a good understanding of ipv4 vs ipv6, and
-
How to Check for Malware on Mac Safely in 2026

If your Mac suddenly slows down or behaves differently, you should not ignore it. Instead, you should understand how to check for malware on Mac because even small issues can point to hidden threats. Most users continue to believe that Macs are totally secure, but contemporary cyber threats have altered this reality. Thus, you will
-
Android vs iOS Security: Real Comparison in 2026

Mobile phones have become a source of personal, financial and professional information. Due to this change, security has turned out to be a daily issue and no longer a technical issue. Individuals do not simply buy a device based on the design or performance of the device. Instead, they scrutinize its effectiveness in safeguarding their
Search
About
Lorem Ipsum has been the industrys standard dummy text ever since the 1500s, when an unknown prmontserrat took a galley of type and scrambled it to make a type specimen book.
Lorem Ipsum has been the industrys standard dummy text ever since the 1500s, when an unknown prmontserrat took a galley of type and scrambled it to make a type specimen book. It has survived not only five centuries, but also the leap into electronic typesetting, remaining essentially unchanged.




